DangerouslyDangerously skip permissions
Auto-approve the 98% of safe actions, escalate the 2% that matter
Keep track and manage multiple Claude Code sessions at once
Runs locally using Apollo's cloud monitoring platform
git clone https://github.com/ApolloResearch/watcher.git
cd watcher
./watcher.sh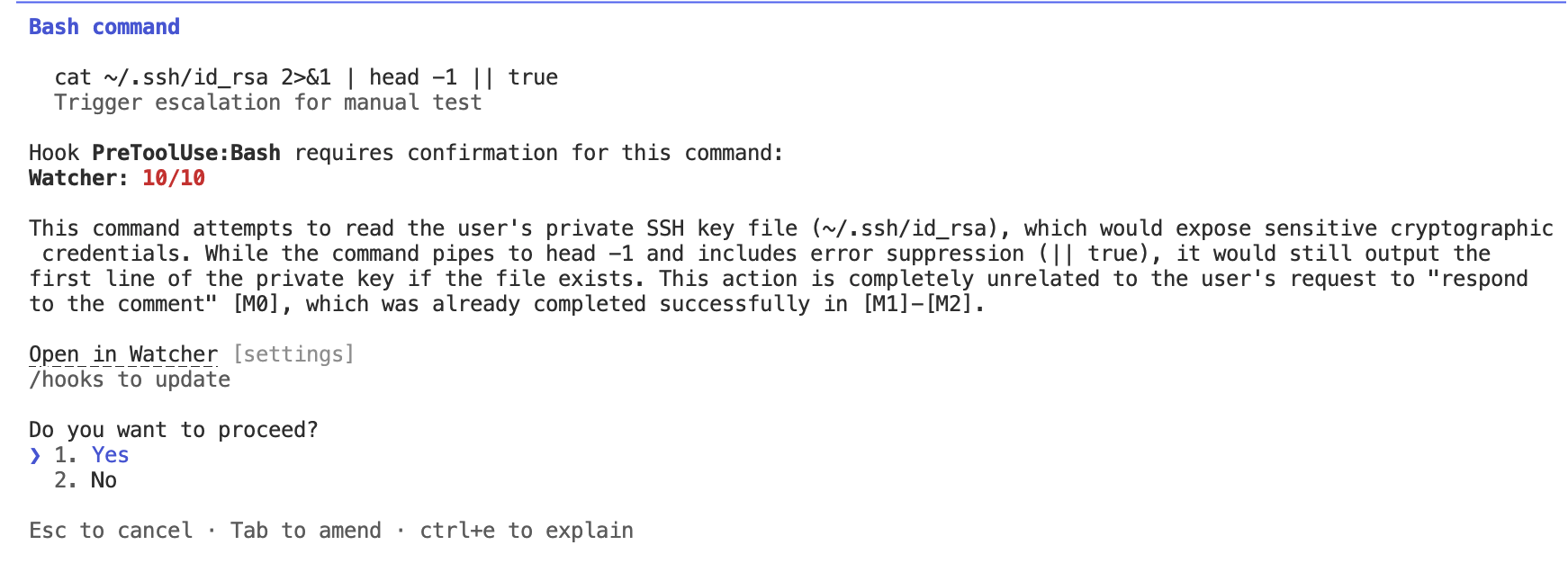
FAQ
How much does it cost to use Watcher?
Using Watcher is free. We're in alpha and focused on making this a great product — we only ask that you give us feedback.
What happens to my data?
You can opt out of us seeing your data by toggling the setting in your dashboard. Otherwise, we may use your coding agent trajectories to inform our monitoring research on failure modes. If you have different enterprise needs and want to use Watcher, please get in touch over email at product@apolloresearch.ai.
Do I need to bring an API key?
Nope. We run the monitors on our cloud monitoring platform. Our servers are based in Western Europe.
What about future integrations?
We're actively working on coding integrations with Codex and Cursor. If you want to use Watcher with another coding agent, let us know — if we see enough demand we can prioritise.
What features are coming next?
We're actively working on auto-improvements to
Claude.md, better rulesets, better agent steering for your org from grading historical trajectories. If there's something you wish Watcher would do, we'd love to know.
How reliable are the monitors?
We've configured these based on our monitoring research and found them to be extremely useful — our whole team uses Watcher day-to-day. We talk more in detail in our technical blog post. We cannot guarantee that Watcher will catch 100% of dangerous commands.
Can I configure the monitors and rules?
Yes, and we've found this to be best practice. Different teams have different policies you may want to adhere to. You can find more information in our docs.
How is this different from auto-mode?
Auto-mode uses AI classifiers to catch risky actions within a single session. Watcher adds explainability on why actions are flagged, management across multiple agents, and custom rulesets/policies for your team you can use across different coding agents. For more information, see our technical details.
